刚接触mongo,希望mongo大佬解惑,感谢。
需求
数据结构中有有个数组`malIps`,这个数组中有个字段`attack`,想对malIps这个数组进行分页,并且不返回`attack`这个数组对象。
mongo中存储的数据结构:
{
"_id" : ObjectId("60ab1cd22119d970838a7db8"),
"attackTypeAmount" : 7,
"logTotal" : 48500,
"attackTotal" : 9758,
"attackTypeTotal" : {
"scanrobots" : 330,
"FileInclude" : 4020,
"Javaouinstream" : 6,
"Sensitivefile" : 4785,
"SQLInjection" : 6,
"Webshell" : 12,
"XSS" : 599
},
"malIpTotal" : 3,
"malIps" : [
{
"attackCounts" : 9758,
"telecomOperator" : "",
"finishTime" : "2020-12-03 16:05:46",
"isMalIp" : false,
"attackTypeAmount" : 9758,
"ip" : "192.168.0.112",
"latitude" : "",
"location" : "",
"startTime" : "2020-12-02 13:55:59",
"attackTypeTotal" : {
"scanrobots" : 330,
"FileInclude" : 4020,
"Javaouinstream" : 6,
"Sensitivefile" : 4785,
"SQLInjection" : 6,
"Webshell" : 12,
"XSS" : 599
},
"longitude" : "",
"attack" : [
{
"dateTime" : "2020-12-03 16:05:46",
"lineNo" : 48224,
"log" : "192.168.0.112 - - [03/Dec/2020:16:05:46 0800] \"GET /noindex/common/css//../../../WEB-INF/web.xml\u0000.jsp HTTP/1.1\" 404 242 \"-\" \"Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.21 (KHTML, like Gecko) Chrome/41.0.2228.0 Safari/537.21\"",
"filePath" : "F:\\test\\logs\\apache\\access_log",
"type" : "Sensitivefile",
"status" : "404"
},
{
"dateTime" : "2020-12-03 16:05:46",
"lineNo" : 48272,
"log" : "192.168.0.112 - - [03/Dec/2020:16:05:46 0800] \"GET /noindex/common/fonts/documents HTTP/1.1\" 404 228 \"-\" \"Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.21 (KHTML, like Gecko) Chrome/41.0.2228.0 Safari/537.21\"",
"filePath" : "F:\\test\\logs\\apache\\access_log",
"type" : "XSS",
"status" : "404"
}
]
},
{
"attackCounts" : 9758,
"telecomOperator" : "",
"finishTime" : "2020-12-03 16:05:46",
"isMalIp" : false,
"attackTypeAmount" : 9758,
"ip" : "192.168.0.113",
"latitude" : "",
"location" : "",
"startTime" : "2020-12-02 13:55:59",
"attackTypeTotal" : {
"scanrobots" : 330,
"FileInclude" : 4020,
"Javaouinstream" : 6,
"Sensitivefile" : 4785,
"SQLInjection" : 6,
"Webshell" : 12,
"XSS" : 599
},
"longitude" : "",
"attack" : [
{
"dateTime" : "2020-12-03 16:05:46",
"lineNo" : 48224,
"log" : "192.168.0.113 - - [03/Dec/2020:16:05:46 0800] \"GET /noindex/common/css//../../../WEB-INF/web.xml\u0000.jsp HTTP/1.1\" 404 242 \"-\" \"Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.21 (KHTML, like Gecko) Chrome/41.0.2228.0 Safari/537.21\"",
"filePath" : "F:\\test\\logs\\apache\\access_log",
"type" : "Sensitivefile",
"status" : "404"
},
{
"dateTime" : "2020-12-03 16:05:46",
"lineNo" : 48300,
"log" : "192.168.0.113 - - [03/Dec/2020:16:05:46 0800] \"GET /noindex/common/images/documents HTTP/1.1\" 404 229 \"-\" \"Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.21 (KHTML, like Gecko) Chrome/41.0.2228.0 Safari/537.21\"",
"filePath" : "F:\\test\\logs\\apache\\access_log",
"type" : "XSS",
"status" : "404"
}
]
},
{
"attackCounts" : 9758,
"telecomOperator" : "",
"finishTime" : "2020-12-03 16:05:46",
"isMalIp" : false,
"attackTypeAmount" : 9758,
"ip" : "192.168.0.114",
"latitude" : "",
"location" : "",
"startTime" : "2020-12-02 13:55:59",
"attackTypeTotal" : {
"scanrobots" : 330,
"FileInclude" : 4020,
"Javaouinstream" : 6,
"Sensitivefile" : 4785,
"SQLInjection" : 6,
"Webshell" : 12,
"XSS" : 599
},
"longitude" : "",
"attack" : [ ]
}
]
}
想得到的数据结构,得到`malIps`的前两条数据,不要`attack`字段,如下:
{
"_id" : ObjectId("60ab1cd22119d970838a7db8"),
"attackTypeAmount" : 7,
"logTotal" : 48500,
"attackTotal" : 9758,
"attackTypeTotal" : {
"scanrobots" : 330,
"FileInclude" : 4020,
"Javaouinstream" : 6,
"Sensitivefile" : 4785,
"SQLInjection" : 6,
"Webshell" : 12,
"XSS" : 599
},
"malIpTotal" : 3,
"malIps" : [
{
"attackCounts" : 9758,
"telecomOperator" : "",
"finishTime" : "2020-12-03 16:05:46",
"isMalIp" : false,
"attackTypeAmount" : 9758,
"ip" : "192.168.0.112",
"latitude" : "",
"location" : "",
"startTime" : "2020-12-02 13:55:59",
"attackTypeTotal" : {
"scanrobots" : 330,
"FileInclude" : 4020,
"Javaouinstream" : 6,
"Sensitivefile" : 4785,
"SQLInjection" : 6,
"Webshell" : 12,
"XSS" : 599
},
"longitude" : ""
},
{
"attackCounts" : 9758,
"telecomOperator" : "",
"finishTime" : "2020-12-03 16:05:46",
"isMalIp" : false,
"attackTypeAmount" : 9758,
"ip" : "192.168.0.113",
"latitude" : "",
"location" : "",
"startTime" : "2020-12-02 13:55:59",
"attackTypeTotal" : {
"scanrobots" : 330,
"FileInclude" : 4020,
"Javaouinstream" : 6,
"Sensitivefile" : 4785,
"SQLInjection" : 6,
"Webshell" : 12,
"XSS" : 599
},
"longitude" : ""
}
]
}
测试用数据插入:
insert({"attackTypeAmount":7,"logTotal":48500,"attackTotal":9758,"attackTypeTotal":{"scanrobots":330,"FileInclude":4020,"Javaouinstream":6,"Sensitivefile":4785,"SQLInjection":6,"Webshell":12,"XSS":599},"malIpTotal":3,"malIps":[{"attackCounts":9758,"telecomOperator":"","finishTime":"2020-12-03 16:05:46","isMalIp":false,"attackTypeAmount":9758,"ip":"192.168.0.112","latitude":"","location":"","startTime":"2020-12-02 13:55:59","attackTypeTotal":{"scanrobots":330,"FileInclude":4020,"Javaouinstream":6,"Sensitivefile":4785,"SQLInjection":6,"Webshell":12,"XSS":599},"longitude":"","attack":[{"dateTime":"2020-12-03 16:05:46","lineNo":48224,"log":"192.168.0.112 - - [03/Dec/2020:16:05:46 0800] \"GET /noindex/common/css//../../../WEB-INF/web.xml\u0000.jsp HTTP/1.1\" 404 242 \"-\" \"Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.21 (KHTML, like Gecko) Chrome/41.0.2228.0 Safari/537.21\"","filePath":"F:\\test\\logs\\apache\\access_log","type":"Sensitivefile","status":"404"},{"dateTime":"2020-12-03 16:05:46","lineNo":48272,"log":"192.168.0.112 - - [03/Dec/2020:16:05:46 0800] \"GET /noindex/common/fonts/documents HTTP/1.1\" 404 228 \"-\" \"Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.21 (KHTML, like Gecko) Chrome/41.0.2228.0 Safari/537.21\"","filePath":"F:\\test\\logs\\apache\\access_log","type":"XSS","status":"404"}]},{"attackCounts":9758,"telecomOperator":"","finishTime":"2020-12-03 16:05:46","isMalIp":false,"attackTypeAmount":9758,"ip":"192.168.0.113","latitude":"","location":"","startTime":"2020-12-02 13:55:59","attackTypeTotal":{"scanrobots":330,"FileInclude":4020,"Javaouinstream":6,"Sensitivefile":4785,"SQLInjection":6,"Webshell":12,"XSS":599},"longitude":"","attack":[{"dateTime":"2020-12-03 16:05:46","lineNo":48224,"log":"192.168.0.113 - - [03/Dec/2020:16:05:46 0800] \"GET /noindex/common/css//../../../WEB-INF/web.xml\u0000.jsp HTTP/1.1\" 404 242 \"-\" \"Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.21 (KHTML, like Gecko) Chrome/41.0.2228.0 Safari/537.21\"","filePath":"F:\\test\\logs\\apache\\access_log","type":"Sensitivefile","status":"404"},{"dateTime":"2020-12-03 16:05:46","lineNo":48300,"log":"192.168.0.113 - - [03/Dec/2020:16:05:46 0800] \"GET /noindex/common/images/documents HTTP/1.1\" 404 229 \"-\" \"Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.21 (KHTML, like Gecko) Chrome/41.0.2228.0 Safari/537.21\"","filePath":"F:\\test\\logs\\apache\\access_log","type":"XSS","status":"404"}]},{"attackCounts":9758,"telecomOperator":"","finishTime":"2020-12-03 16:05:46","isMalIp":false,"attackTypeAmount":9758,"ip":"192.168.0.114","latitude":"","location":"","startTime":"2020-12-02 13:55:59","attackTypeTotal":{"scanrobots":330,"FileInclude":4020,"Javaouinstream":6,"Sensitivefile":4785,"SQLInjection":6,"Webshell":12,"XSS":599},"longitude":"","attack":[]}]});
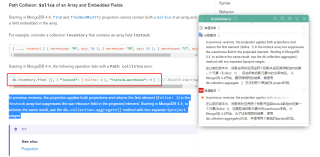
查了官方文档,find 和 slice好像实现不了,需要用aggregate() 并使用两个单独的$project可是官方没有对应的例子,咋都凑不出来。